In March, Tom Byrne was speaking at the Cephalocon APAC 2018 Conference in Beijing, aimed at Ceph users and developers. He presented SCD's work using Erasure Coding on Ceph to store data from the LHC experiments at CERN. With a usable capacity of approximately 10PB our Echo cluster is one of the largest systems of its kind, set to expand further over the coming years.
"We use Ceph in a different way to others in the High Energy and Physics Community," said Tom. "My talk highlighted this and also gave an opportunity to draw attention to some of the cjhallenges this has presented."
Following his presentation, Tom was invited to discuss his experiences with Sage Weil, the founder and chief architect of the Ceph distributed storage platform. They are now collaborating to work out how the system can be improved to help us, and others, manage erasure coded Ceph clusters at scale.
Meanwhile Rob Appleyard and Catalin Condurache were at the International Symposium on Grids and Clouds (ISGC) 2018, held in Taipei, which had a main theme of “Understanding Open Data: Challenges and Opportunities in the Deep Learning Era". Their talks focused on how we are dealing with demands for future storage and computing needs.
Rob said, "ISGC is unlike many other conferences we go to – it's a very cosmopolitan computing conference with a broad focus and people from lots of different fields. There's a regular group of (mostly) Europeans from the Worldwide LHC Computing Grid community who know each other, and many talks come from that WLCG perspective, but there's also many, many other topics being discussed"
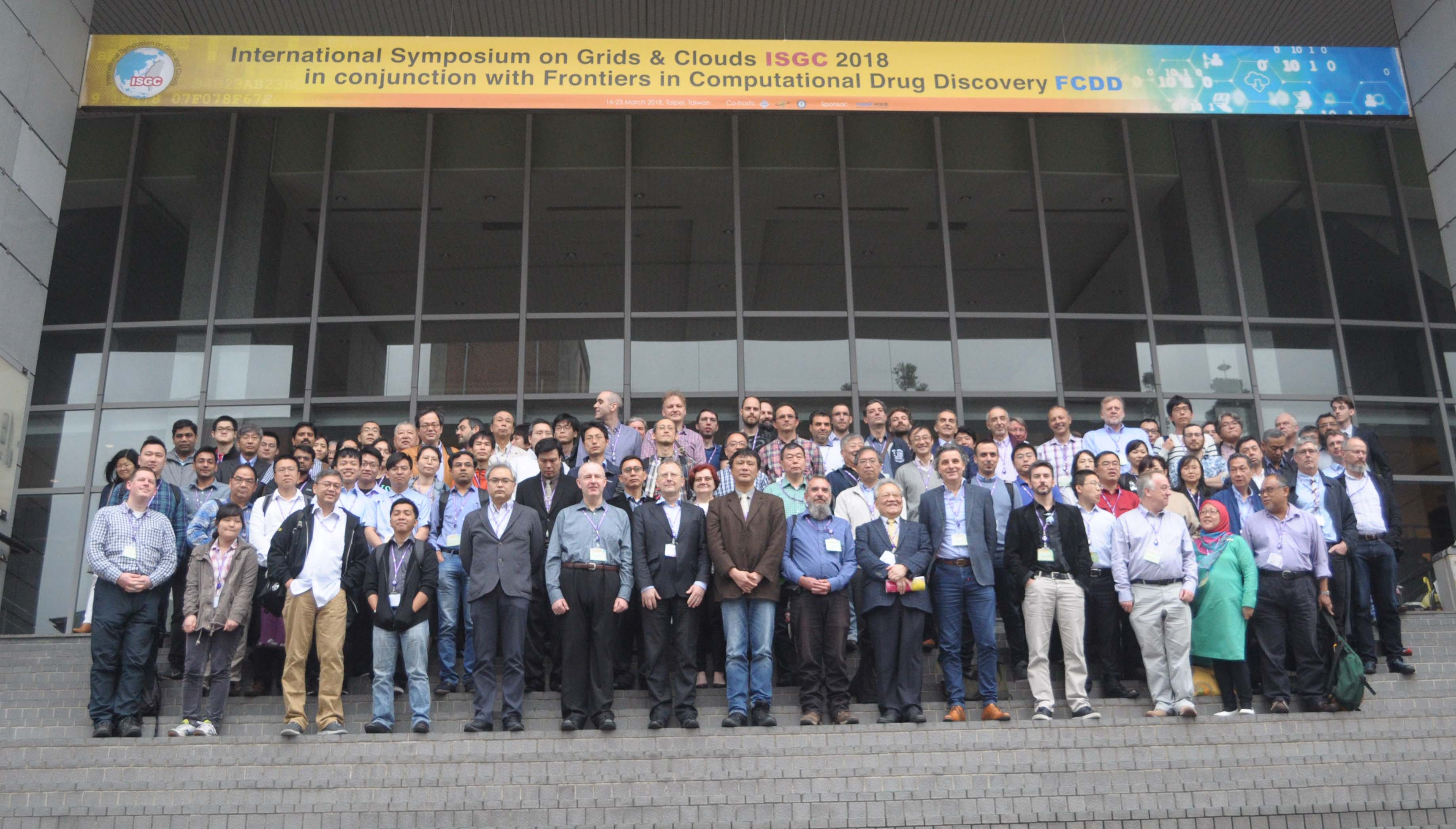 Rob gave two presentations - the first was on future plans for downsizing our CASTOR storage system . The second was about our new Ceph storage system and our experiences of hard disk management.
Rob gave two presentations - the first was on future plans for downsizing our CASTOR storage system . The second was about our new Ceph storage system and our experiences of hard disk management.
He also spent time talking with the two lead computing people from the LHCb experiment at CERN about the future of CERN software; and he made a new contact - a professor who works on volunteer computing for the ATLAS experiment.
"At the Institute of High Energy Physics (IHEP) in Beijing they have a system that uses software which is written for a volunteer computer scheme, known as BOINC, to use excess capacity on their Central Processing Unit farm," said Rob. "When the 'main' job on a node is waiting on something that doesn't need the CPU, like copying data around, the BOINC job uses the spare CPU time."
Catalin Condurache spoke about the CernVM-FS (File System) and its status; and the latest developments from the STFC Rutherford Appleton Laboratory (RAL) Tier-1 perspective. This technology is now the standard method used for experiment software distribution across Grid and Cloud environments by various scientific communities (High Energy Physics, Space, Natural and Life Sciences).
"I took the opportunity to meet colleagues from IHEP in China and Academia Sinica in Taiwan and discuss more specifically about the technical implementation of the 'confidential' CernVM-FS repositories in Asia," said Catalin. "Overall it was a very good occasion for me to disseminate information about my work at RAL, and to consolidate relations with partners from other organisations for further collaborations."
Some of the interesting conference sessions which Rob and Catalin attended were:
- A talk by Dr. Sadakazu Haino from Academia Sinica (the host institution) on the computing challenges of gravitational wave detection.
- An overview of cryo-electron microscopy by Dr. Matthias Wolf from the Okinawa Institute of Science and Technology, including how they plan to use grid computing to solve some of their upcoming data issues.
- A workshop on computer security which included a very useful overview of the current security landscape and how powerful malicious software can be at the moment. It focused on the basics of secure system administration with emphasis on virtual machines in a federated Cloud infrastructure. Presentations included typical attacks on systems, as well as the various ways criminals monetize systems they gained control over. There was also a worked exercise on performing forensics after an attack.